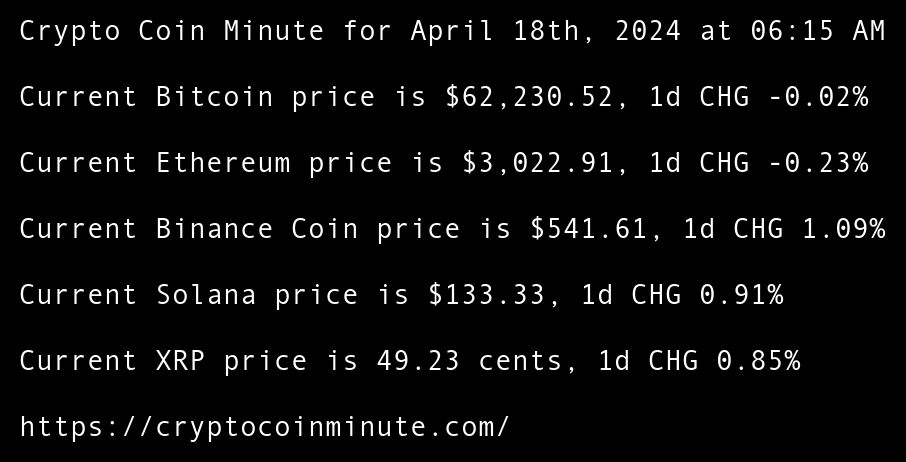
Crypto Coin Minute for April 18th, 2024 at 06:15 AM Pacific Time.
Current Bitcoin price is $62,230.52, 1d CHG -0.02% Current Ethereum price is $3,022.91, 1d CHG -0.23% Current Binance Coin price is $541.61, 1d CHG 1.09% Current Solana price is $133.33, 1d CHG 0.91% Current XRP price is 49.23 cents, 1d CHG 0.85% Worldcoin unveils World
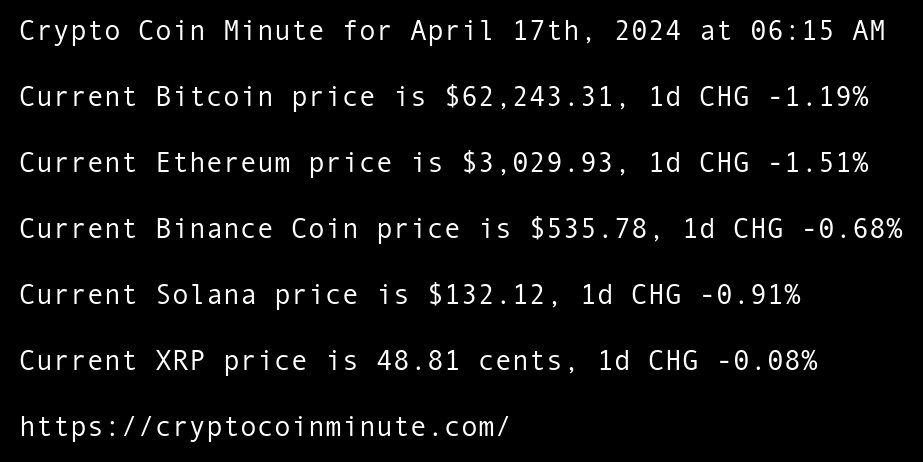
Crypto Coin Minute for April 17th, 2024 at 06:15 AM Pacific Time.
Current Bitcoin price is $62,243.31, 1d CHG -1.19% Current Ethereum price is $3,029.93, 1d CHG -1.51% Current Binance Coin price is $535.78, 1d CHG -0.68% Current Solana price is $132.12, 1d CHG -0.91% Current XRP price is 48.81 cents, 1d CHG -0.08% Max Boonen’s PV01
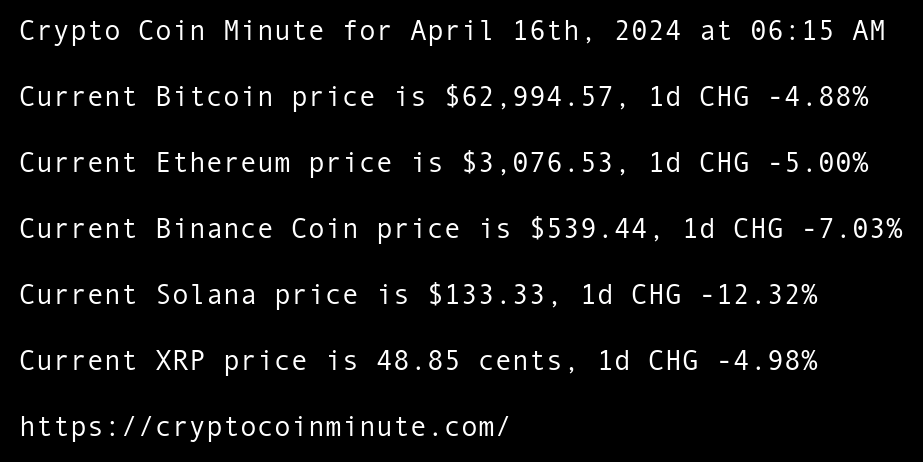
Crypto Coin Minute for April 16th, 2024 at 06:15 AM Pacific Time.
Current Bitcoin price is $62,994.57, 1d CHG -4.88% Current Ethereum price is $3,076.53, 1d CHG -5.00% Current Binance Coin price is $539.44, 1d CHG -7.03% Current Solana price is $133.33, 1d CHG -12.32% Current XRP price is 48.85 cents, 1d CHG -4.98% HSBC to Expand
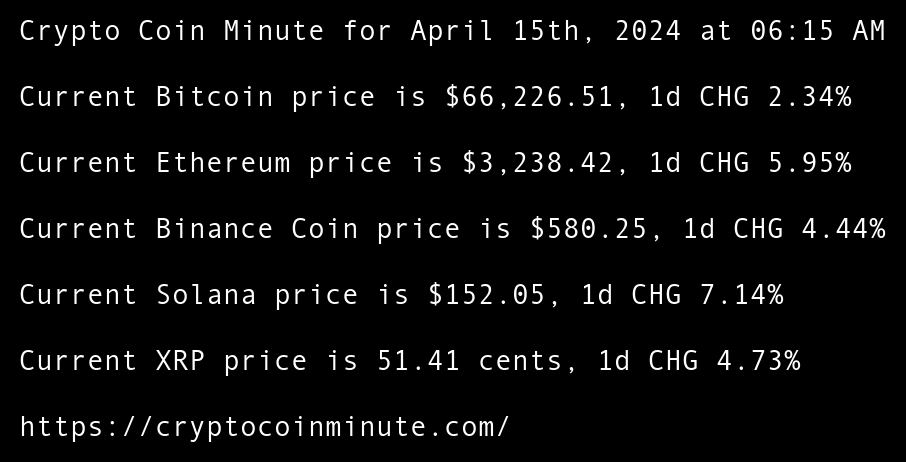
Crypto Coin Minute for April 15th, 2024 at 06:15 AM Pacific Time.
Current Bitcoin price is $66,226.51, 1d CHG 2.34% Current Ethereum price is $3,238.42, 1d CHG 5.95% Current Binance Coin price is $580.25, 1d CHG 4.44% Current Solana price is $152.05, 1d CHG 7.14% Current XRP price is 51.41 cents, 1d CHG 4.73% Vitalik Buterin advocates
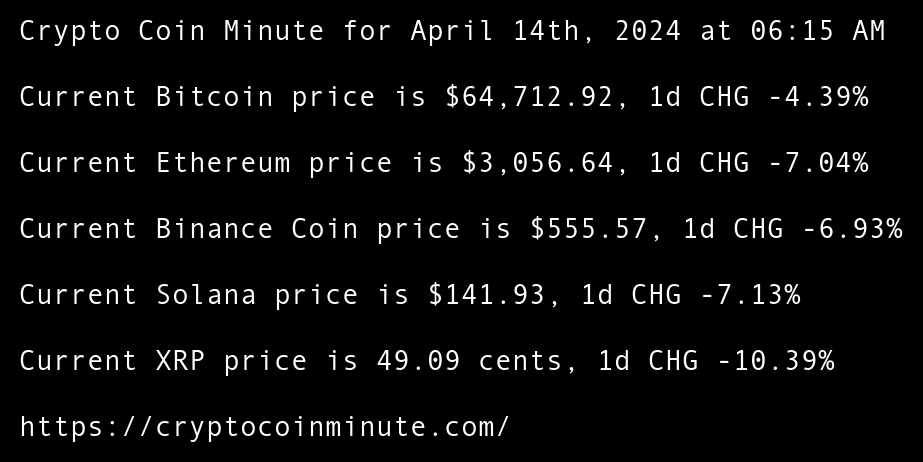
Crypto Coin Minute for April 14th, 2024 at 06:15 AM Pacific Time.
Current Bitcoin price is $64,712.92, 1d CHG -4.39% Current Ethereum price is $3,056.64, 1d CHG -7.04% Current Binance Coin price is $555.57, 1d CHG -6.93% Current Solana price is $141.93, 1d CHG -7.13% Current XRP price is 49.09 cents, 1d CHG -10.39% Argentinas economy is
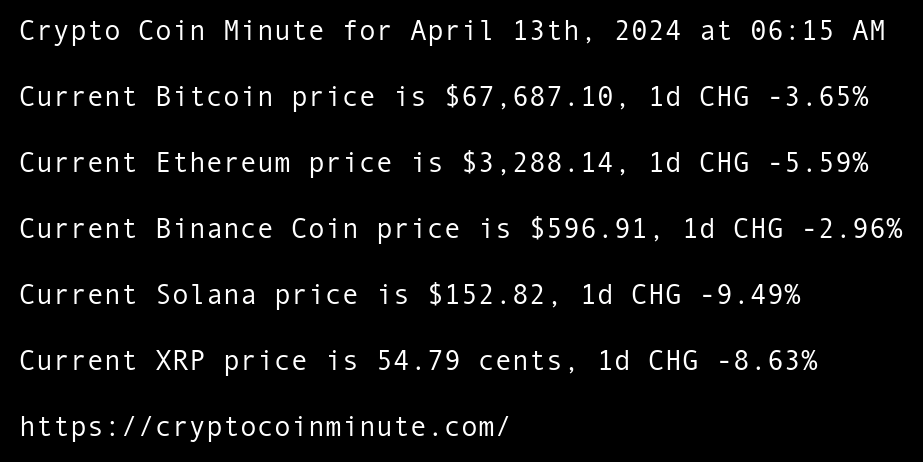
Crypto Coin Minute for April 13th, 2024 at 06:15 AM Pacific Time.
Current Bitcoin price is $67,687.10, 1d CHG -3.65% Current Ethereum price is $3,288.14, 1d CHG -5.59% Current Binance Coin price is $596.91, 1d CHG -2.96% Current Solana price is $152.82, 1d CHG -9.49% Current XRP price is 54.79 cents, 1d CHG -8.63% US Lawmakers Not